How To Stop & Fix An SEO Spambot Site Attack

Spambot attacks are on the rise, with 25.6% Of all Internet traffic coming from a bad bot, increasingly sophisticated methods are used to circumvent common security measures.
Businesses and small websites alike should prevent SEO software from derailing your optimization efforts and causing a sharp drop in traffic and revenue.
If you have been the victim of an attack, you will find the steps here to recover and restore your ranking.
You will also learn about intelligent prevention systems and high level monitoring.
What is a SEO spambot attack?
SEO spambots are very much like friendly Googlebots that want to crawl your site. However, instead of indexing your content, these bots will use vulnerabilities to hack your website.
Why?
They engage in spamdexing.
Essentially, these spam attacks will use your site to try to rank content that could not be ranked otherwise. Hacker bots generate a lot of revenue, and their spamming tactics cause your site to experience a huge drop in SEO and revenue.
In addition, black hat SEO techniques are used to disguise the attack.
Some of the more infamous things a spambot can do are:
- Spam.
- Content scraping.
- Sniff the credentials.
- SQL entries to update parts of the site.
- Link inserts.
- Obstetric reorientation.
- Unwanted Google Analytics.
- Spam User Generated Content (UGC).
Often the main goal of spam is to insert links into your website. Hidden links will help boost hacker’s website and revenue while damaging your site.
We’ve also seen redirects generated to generate false URLs that redirect to the hacker’s website.
In each of these cases, the spambot is taking advantage of the site for its own gain.
Sometimes display ads are inserted into a site using SQL injections, but most of these infiltrations are about links or redirects to a website that, in some way, is making money.
Learn about the SEO spambot attack
Spambots work hard to circumvent normal detection methods. Links are included or pages are created to hide them from the site owner.
Sometimes, you will find that your CMS has underlying vulnerabilities, and that you are just another victim of an attack.
However, there are some warning signs that something is wrong:
- decrease in traffic.
- Random website pages.
- GSC Warnings.
- Google search warnings.
Businesses and more established websites will have multiple forms of disclosure, such as:
- Firewalls.
- recording systems.
- monitoring systems.
If you’re running WordPress, there are basic vulnerabilities that hackers will discover and use to their advantage.
Attacks on your site can be diagnosed using plugins like MalCare or Wordfence, both of which add multiple layers of security to your site.
In addition, you can use Cloudflare to take preventative measures to stop bots in their tracks with a bot management system.
A step-by-step guide to treating a spambot attack
Spambot remediation requires a few steps that will help you stop the attack and restore your site.
1. Prevent bots from doing additional damage
For the next two steps, your site will remain vulnerable until you determine how the spambot accessed your site and caused damage. Therefore, before scanning your site, you will need to put bot protection in place.
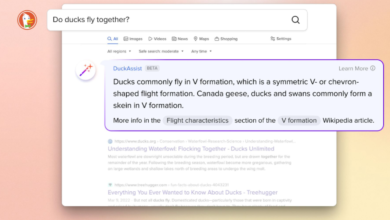
Cloudflare’s bot management system uses artificial intelligence and machine learning to stop bad bots.
The tool will use a three-pronged approach to provide real-time protection:
- behavioral analysis It will be used to detect any traffic anomalies.
- machine learning It will use billions of data points to accurately detect bots.
- fingerprints They will also be used to classify previously detected bots.
Rich analytics and logs will add to your site’s security and save you time to clean up your site.
2. Perform a site scan to identify affected pages
Now that your site has a high level of protection to stop additional spambot attacks, it’s time to run a scan on your site. We use the word “wiping” very broadly because you can:
- Run an analytics report to see which pages your site traffic has dropped the most.
- Run a scan with Screaming Frog or something similar.
- FTP on your site and search folders for manually created pages.
You can even manually go through each page on your site, looking at the source code for pages that may contain hidden links.
Screaming Frog will help you find hidden redirects.
If you have logs available, be sure to analyze them to see where the traffic is coming from and to find any pages on the site that may have been generated by a bot.
A lot of time will be spent deciding what to clean up on the site.
3. Find out how the site was hacked
Secure sites are not hacked. For the most part, attacks from spambots look for existing vulnerabilities that you haven’t patched. Websites may have been hacked for the following reasons:
- Bad plugins.
- old program.
- SQL injection.
- FTP / Admin passwords are easy to guess.
Your first step is to make sure that all software and plugins on your site are updated. Old scripts should be updated, and if you notice scripts that you did not create, delete them.
Hackers may leave a script on your server to regain access to your site in the future.
It is recommended that you work with someone to go through your logs and discover how the attack occurred.
You want to patch these vulnerabilities before you follow these steps. Cloudflare should add an extra layer of protection, too.
4. Clean the top pages first
Cleaning your site depends on the type of attack that occurred. If your site has user generated spam pages or mass generated pages, you will need to do the tedious task of determining which pages are needed and which are spam.
You will then need to delete these spam generated pages.
However, you also want to do a few important things for pages that aren’t generated by spam:
- Analyze your analytics.
- Mark the most affected pages.
- Start by cleaning your first pages first.
You must first work on your revenue generating pages to help restore their rankings.
When we say “work”, you’ll need to scroll through all of these pages thoroughly to find:
- redirects.
- hidden links.
- Ads or malicious code.
Normally, you would need to manually clean and review each page.
Even if a link is simply inserted into your site’s footer, you’ll still want to check all of your pages to make sure there’s nothing else you’re missing on each page.
Once you are sure that all spam is removed, it will be a waiting game to see what happens to your rankings.
5. Monitor the site
Monitoring your site should become part of your daily operations. You’ll want to monitor your site in several ways:
- Monitor your rankings and analytics for any changes.
- Monitor website logs for any suspicious activity.
You must determine how the attack occurred and the entry point. However, there are times when a spambot will put a backdoor on your server, come back and mess everything up – again.
It is imperative that you continue to monitor your site for suspicious activity so that you can address issues quickly.
6. Optional: Restore from backup
If you are very lucky and attack early, you may be able to roll back your site with a snapshot. However, if you have new customer orders or data inserted into affected databases, this method will not work.
Unfortunately, your backups will still contain the original vulnerabilities that led to a successful attack.
At this point, your best bet is to restore the site using Cloudflare protection and then patch the main attack vulnerabilities.
If the attack goes unnoticed for weeks or months, your backups may already have been compromised, making this solution unusable.
Final thoughts
Spambots are dangerous because they can remain undetected for long periods of time. If a bot slips through and inserts links or content into existing pages, it can quickly ruin your company’s reputation and hamper your SEO efforts.
In addition, these link entries are often a word or two associated with the site, and the text is built on Not Looks like a link.
Recognizing an attack of this type can be very difficult.
We’ve also seen spambots create thousands of pages on a site, using actual files, so new posts never show up in the CMS dashboard.
It took a full two months to get rid of spam at this level, so there was a lot of damage to the customer’s website.
Stopping a spambot SEO attack requires attention to detail and intense monitoring. Cloudflare is a good option along with multiple levels of firewalls, logging and monitoring systems to thwart spambot attacks.
You’ll also need to think about user controls and access and work on other ways to harden your website’s server.
More resources:
- How to protect your WordPress site from hackers
- HTTP or HTTPS? Why do you need a secure website
- WordPress SEO Guide: Everything You Need To Know
Featured image: Tatyana Shepeleva/Shutterstock